Has your WordPress website been hacked?
Hackers will often install a backdoor to make sure they can get back in even after you secure your website. Unless you can remove that backdoor, there’s no stopping them.
In this article, we’ll show you how to find a backdoor in a hacked WordPress site and fix it.
How to Tell if Your Website Has Been Hacked
If you are running a WordPress website, then you need to take security seriously. That’s because websites are attacked an average of 44 times every day.
You can learn best practices to keep your site safe in our ultimate WordPress security guide.
But what if your site has already been hacked?
Some signs your WordPress site has been hacked include a drop in website traffic or performance, added bad links or unknown files, a defaced home page, an inability to log in, suspicious new user accounts, and more.
Cleaning up a hacked website can be incredibly painful and difficult. We take you through the process step by step in our beginner’s guide to fixing your hacked WordPress site. You should also make sure you scan your site for any malware that the hackers left.
And don’t forget to close the backdoor.
A smart hacker knows that you’ll eventually clean up your website. The first thing they might do is install a backdoor, so they can sneak back in after you secure the front door to your WordPress website.
What Is a Backdoor?
A backdoor is code added to a website that allows a hacker to access the server while remaining undetected, and bypassing the normal login. It allows a hacker to regain access even after you find and remove the exploited plugin or vulnerability to your website.
Backdoors are the next step of a hack after the user has broken in. You can learn how they may have done that in our guide on how WordPress sites get hacked and how to prevent it.
Backdoors often survive WordPress upgrades. That means your site will remain vulnerable until you find and fix every backdoor.
How Do Backdoors Work?
Some backdoors are simply hidden admin usernames. They let the hacker log in as normal by typing a username and password. Because the username is hidden, you’re not even aware that someone else has access to your website.
More complex backdoors can allow the hacker to execute PHP code. They manually send the code to your website using their web browser.
Others have a full fledged user interface that allows them to send emails as your WordPress hosting server, execute SQL database queries, and much more.
Some hackers will leave more than one backdoor file. After they upload one, they will add another to ensure their access.
Where Are Backdoors Hidden?
In every case we’ve found, the backdoor was disguised to look like a WordPress file. The code for backdoors on a WordPress site are most commonly stored in the following locations:
- A WordPress theme, but probably not the the one you’re currently using. Code in a theme is not overwritten when you update WordPress, so it’s a good place to put a backdoor. That’s why we recommend deleting all inactive themes.
- WordPress plugins are another good place to hide a backdoor. Like themes, they’re not overwritten by WordPress updates, and many users are reluctant to upgrade plugins.
- The uploads folder may contain hundreds or thousands of media files, so it’s another good place to hide a backdoor. Bloggers almost never check its contents because they just upload an image and then use it in a post.
- The wp-config.php file contains sensitive information used to configure WordPress. It’s one of the most highly targeted files by hackers.
- The wp-includes folder contains PHP files required for WordPress to run properly. It’s another place that we find backdoors because most website owners don’t check to see what the folder contains.
Examples of Backdoors We’ve Found
Here are some examples of where hackers have uploaded backdoors. In one site we cleaned up, the backdoor was in the wp-includes folder. The file was called wp-user.php, which looks innocent enough, but that file doesn’t actually exist in a normal WordPress installation.
In another instance, we found a PHP file named hello.php in the uploads folder. It was disguised as the Hello Dolly plugin. What’s strange is that the hacker put it in the uploads folder instead of the plugins folder.
We’ve also found backdoors that don’t use the .php file extension. One example was a file named wp-content.old.tmp, and we’ve also found backdoors in files with a .zip extension.
As you can see, hackers can take very creative approaches when hiding a backdoor.
In most cases, the files were encoded with Base64 code that can perform all sorts of operations. For example, they can add spam links, add additional pages, redirect the main site to spammy pages, and more.
With that being said, let’s take a look at how to find a backdoor in a hacked WordPress site and fix it.
How to Find a Backdoor in a Hacked WordPress Site and Fix It
Now you know what a backdoor is and where it might be hidden. The difficult part is finding it! After that, cleaning it up is as easy as deleting the file or code.
1. Scan for Potentially Malicious Code
The easiest way to scan your website for backdoors and vulnerabilities is with a WordPress malware scanner plugin. We recommend Securi because it helped us block 450,000 WordPress attacks in 3 months, including 29,690 backdoor related attacks.
They offer a free Sucuri Security plugin for WordPress that lets you scan your website for common threats and harden your WordPress security. The paid version includes a server side scanner that runs once each day and looks for backdoors and other security issues.
Learn more in our guide on how to scan your WordPress site for potentially malicious code.
2. Delete Your Plugins Folder
Searching through your plugin folders looking for suspicious files and code is time consuming. And because hackers are so sneaky, there’s no guarantee you will find a backdoor.
The best thing you can do is delete your plugins directory, and then reinstall your plugins from scratch. This is the only way to know for sure that there are no backdoors in your plugins.
You can access your plugins directory using an FTP client or your WordPress host’s file manager. If you haven’t used FTP before, then you may want to see our guide on how to use FTP to upload files to WordPress.
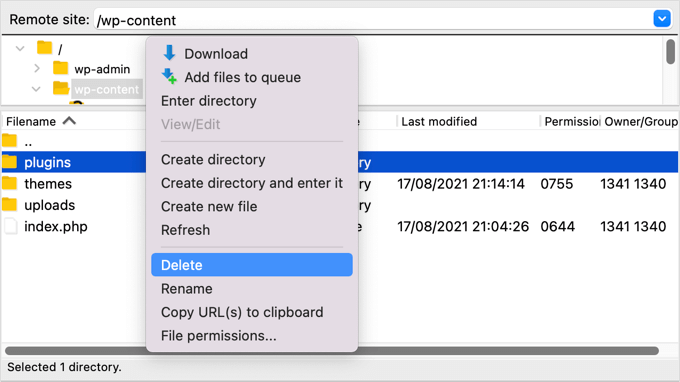
You will need to use the software to navigate to your website’s wp-content folder. Once there, you should right click on the plugins folder and select ‘Delete’.
3. Delete Your Themes Folder
In the same way, instead of spending time searching for a backdoor among your theme files, it’s better just to delete them.
After you delete your plugin folder, simply highlight the themes folder and delete it in the same way.
You don’t know whether there was a backdoor in that folder, but if there was, it’s gone now. You just saved time and you eliminated an extra point of attack.
Now you can reinstall any themes that you need.
4. Search the Uploads Folder for PHP Files
Next, you should take a look through the uploads folder and make sure that there are no PHP files inside.
There is no good reason for a PHP file to be in this folder because it’s designed to store media files such as images. If you find a PHP file there, then it should be deleted.
Like the plugins and themes folders, you’ll find the uploads folder in the wp-content folder. Inside the folder you will find multiple folders for each year and month you have uploaded files. You will need to check each folder for PHP files.
Some FTP clients offer tools that will search the folder recursively. For example, if you use FileZilla, then you can right click the folder and select ‘Add files to queue’. Any files found in any subdirectories of the folder will be added to the queue in the bottom pane.
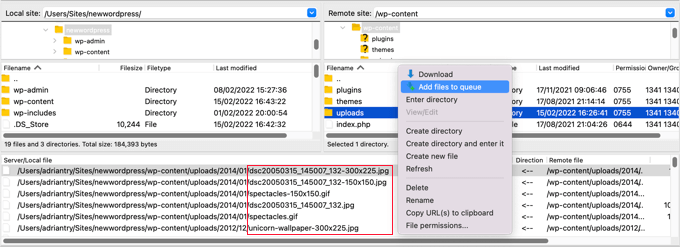
You can now scroll through the list looking for files with the .php extension.
Alternatively, advanced users who are familiar with SSH can write the following command:
find uploads -name "*.php" -print
5. Delete the .htaccess File
Some hackers may add redirect codes to your .htaccess file that will send your visitors to a different website.
Using an FTP client or file manager, simply delete the file from your website’s root directory, and it will be recreated automatically.
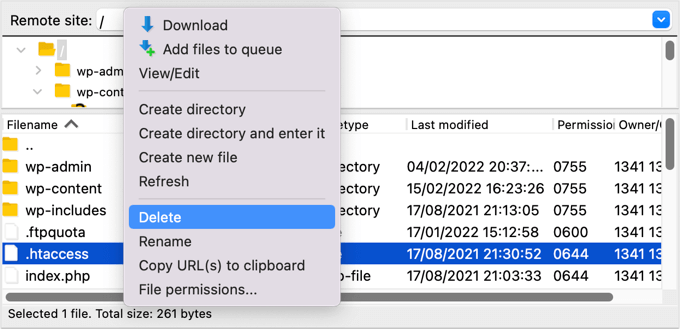
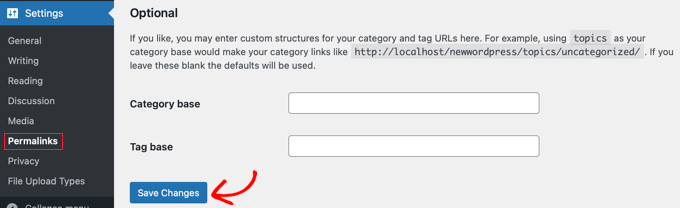
If for some reason it isn’t recreated, then you should go to Settings » Permalinks in your WordPress admin panel. Clicking the ‘Save Changes’ button will save a new .htaccess file.
6. Check the wp-config.php File
The wp-config.php file is a core WordPress file that contains information that allows WordPress to communicate with the database, the security keys for your WordPress installation, and developer options.
The file is found in your website’s root folder. You can view the file’s contents by selecting the Open or Edit options in your FTP client.
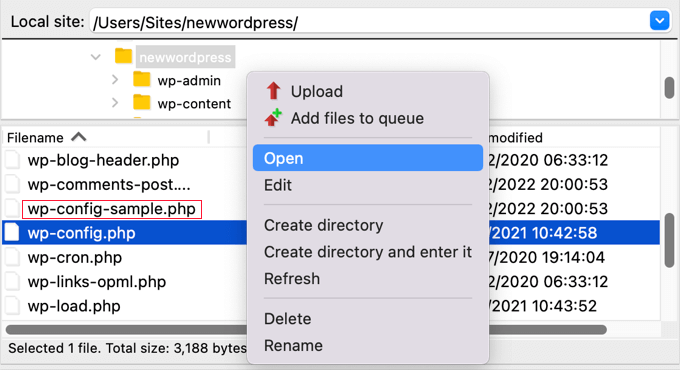
Now you should look at the contents of the file carefully to see if there is anything that looks out of place. It might be helpful to compare the file with the default wp-config-sample.php file which is located in the same folder.
You should delete any code that you’re certain doesn’t belong.
7. Restore a Website Backup
If you have been making regular backups of your website and are still concerned that your website isn’t completely clean, then restoring a backup is a good solution.
You will need to completely delete your website and then restore a backup that was taken before your website was hacked. This isn’t an option for everyone, but it will leave you 100% confident that your site is safe.
For more information, see our beginner’s guide on how to restore WordPress from backup.
How to Prevent Hacks in the Future?
Now that you’ve cleaned up your website, it’s time to improve your site’s security to prevent hacks in the future. It doesn’t pay to be cheap or apathetic when it comes to website security.
1. Regularly Backup Your Website
If you don’t already make regular backups of your website, then today is the day to start.
WordPress does not come with a built-in backup solution. However, there are several great WordPress backup plugins which allow you to automatically backup and restore your WordPress website.
UpdraftPlus is one of the best WordPress backup plugins. It allows you to setup automatic backup schedules and will help you restore your WordPress site if something bad happens.
Learn more in our guide on how to backup and restore your WordPress site with UpdraftPlus.
2. Install a Security Plugin
You can’t possibly monitor everything that goes on your website when you’re busy working on your business. That’s why we recommend you use a security plugin like Sucuri.
We recommend Sucuri because they’re good at what they do. Major publications like CNN, USA Today, PC World, TechCrunch, The Next Web, and others agree. Plus, we rely on it ourselves to keep WPExperiencecoder secure.
3. Make WordPress Login More Secure
It’s also important that you make your WordPress login more secure. The best way to start is to enforce the use of strong passwords when users create an account on your website. We also recommend you start using a password manager utility like 1Password.
The next thing you should do is add two-factor authentication. This will protect your website against stolen passwords and brute force attacks. It means that even if a hacker knows your username and password, they still won’t be able to log in to your website.
Finally, you should limit login attempts in WordPress. WordPress allows users to enter passwords as many times as they want. Locking a user out after five failed login attempts will significantly reduce a hacker’s chance of working out your login details.
4. Protect Your WordPress Admin Area
Protecting the admin area from unauthorized access allows you to block many common security threats. We have a long list of tips on how you can keep WordPress admin safe.
For example, you can password protect the wp-admin directory. This adds another layer of protection to the most important entry point to your website.
You can also limit access to the admin area to the IP addresses used by your team. This is another way to lock out hackers who discover your username and password.
5. Disable Theme and Plugin Editors
Did you know that WordPress comes with a built-in theme and plugin editor? This plain text editor allows you to edit your theme and plugin files directly from the WordPress dashboard.
While this is helpful, it can lead potential security issues. For example, if a hacker breaks into your WordPress admin area, then they can use the built-in editor to gain access to all your WordPress data.
After that, they will be able to distribute malware or launch DDoS attacks from your WordPress website.
To improve WordPress security, we recommend removing the built-in file editors completely.
6. Disable PHP Execution in Certain WordPress Folders
By default, PHP scripts can be run in any folder on your website. You can make your website more secure by disabling PHP execution in folders that don’t need it.
For example, WordPress never needs to run code stored in your uploads folder. If you disable PHP execution for that folder, then a hacker won’t be able to run a backdoor even if they successfully uploaded one there.
7. Keep Your Website Up to Date
Every new version of WordPress is safer than the previous one. Whenever a security vulnerability is reported, the core WordPress team works diligently to release an update that fixes the issue.
This means that if you are not keeping WordPress up to date, then you are using software with known security vulnerabilities. Hackers can search for websites running the older version and use the vulnerabilty to gain access.
That’s why you should always use the latest version of WordPress.
Don’t just keep WordPress up to date. You need to make sure that you also keep your WordPress plugins and themes current.
We hope this tutorial helped you learn how to find and fix a backdoor in a hacked WordPress website. You may also want to learn how to move WordPress from HTTP to HTTPS, or check out our list of WordPress errors and how to fix them.
If you liked this article, then please subscribe to our YouTube Channel for WordPress video tutorials. You can also find us on Facebook and Facebook.
The post How to Find a Backdoor in a Hacked WordPress Site and Fix It first appeared on WPExperiencecoder.